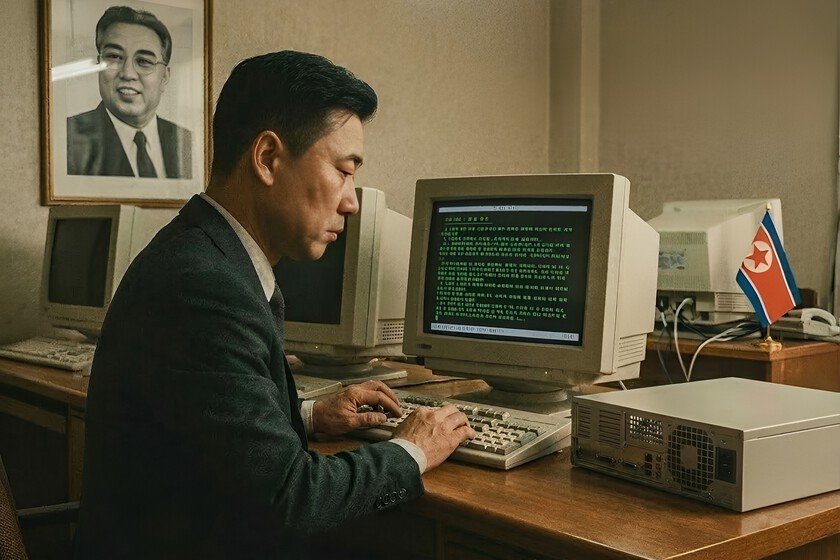
It was a triple trap designed by North Korean hackers
A Spanish blockchain developer was almost a victim of one of the cyber espionage operations more sophisticated ones circulating right now. The bait they used was something as innocent as a job offer sent via LinkedIn. Which It seemed like a professional opportunity. It was actually a trap designed by one of the hacker groups most dangerous north koreans and best financed in the world. The case was analyzed by Claudio Chifafounder of cybersecurity company DLTCodeand coincides with another attack documented a few weeks before vs. Chris PapathanasiouCEO of security firm AllSecure. Two almost identical attacks, two different countries, the same perpetrator: the Lazarus groupthe unit of government digital operations from North Korea. The job offer had a cat in the bag In the Spanish case, the contact came in the form of something as common in the LinkedIn environment as a job offer as a strategic advisor in a decentralized video game project with 100% remote work and flexible hours. After a brief conversation, the supposed recruiter sent a link to advance the hiring process by calling the candidate for a 45-minute video call. After that initial conversation, the bait that would have completed the trap came into play: downloading a repository and opening it in Visual Studio Code to review it. In the case of Papathanasiou, the modus operandi was virtually identical: A LinkedIn profile offered him a job at a company it described as “a rapidly growing team developing the first decentralized AI operating system,” also with a Calendly link (a meeting scheduling tool) to schedule the call. During the video call, the supposed selection manager briefly used the camerashowing a face that matched the LinkedIn profile which he was using as a cover, although the voice did not fit with public videos of that person that Papathanasiou later found. “I started recording mid-conversation once I became suspicious,” said Papathanasiou, who suspects the attackers used surveillance technology. deepfake for impersonate the identity of your interlocutor. Claudio Chifa, on the other hand, became suspicious due to the sum of small details that did not quite fit with the project they were offering him: “The interlocutor’s accent had nothing to do with Portugal, the instructions in the GitHub repository were clearly generated with some AI, which also made me doubt the quality of the project. But, above all, it was the insistence on releasing the code on my machine for an advisory position,” the cybersecurity expert stressed. Three traps in one shot Both the repository analyzed by Chifa and DLTCode and the one investigated by AllSecure hid three independent infection mechanismsdesigned to be activated simultaneously when the folder was opened, so that, if one failed, the other two acted as a backup, completing the job. The first took advantage of a feature in Visual Studio Code that allows you to configure automatic tasks when opening a project. The malicious command was executed in a hidden window, leaving no trace visible to the user, and could adapt to the victim’s operating system (Mac, Linux or Windows). The second mechanism operated during the usual project installation process using npm (the package manager or component installation tool used by JavaScript programmers). At that time, the attacker’s server automatically received all the credentials stored in the system, including keys from services such as AWS, Stripe or OpenAI, and took full control of the computer. The third front of attack was linked to the previous two, so that it was enough to open the folder for all three will be fired at the same time and take their respective positions. “The smartest thing about this attack is that it does not depend on the victim do anything extraordinary. They don’t ask you to run an .exe, they don’t ask you to deactivate the antivirus, they don’t ask you to do anything that activates your alarms. They ask you to open a folder in your code editor. Something that a developer does fifty times a day,” highlights Chifa. Designed to leave no trace The history of the repository analyzed by DLTCode reveals that the operation has been active since September 2025, with eleven control servers from which the attackers manage malware remotely rotated throughout that period. When AllSecure attempted to analyze its attack from AWS servers, Lazarus operators detected that the source IP belonged to a data center and immediately severed the connection. That doesn’t give you an idea of the level of active surveillance this group has over its own infrastructure. The final objective of both attacks was the same: steal cryptocurrency walletsbrowser passwords, SSH keys (remote server access codes) and any stored credentials in the system that may be useful to them in the future. The FBI esteem that the Lazarus group has accumulated more than $1.5 billion stolen in cryptocurrencies through campaigns of this type. How to defend yourself against these types of attacks What saved Chifa from falling into Lazarus’s trap was stop to analyze the code before executing it. Something about the meeting didn’t add up to him and he decided to investigate first. Papathanasiou did the same and, under suspicion, created an isolated virtual environment and analyzed the repository from there instead of opening it directly on his computer. For programmers and software engineers, who have become the main target of these cybercriminals, experts recommend disabling automatic task execution in Visual Studio Code, always inspect the configuration and installation files of any project received externally, and never run code of unknown origin outside of an isolated environment. “The most important precaution is to distrust any selection process that asks you to run code during the first contacts. No legitimate company needs you to open a local repository on the first call. If someone contacts you on LinkedIn with an extraordinary project and a few days later they are asking you to download code, that is the time to stop,” warns the founder of DLTCode. If you suspect an attempt to attack in Spainboth the National Cybersecurity Institute (INCIBE) … Read more