Russia has shown on video how to hunt drones with shotguns. And he has also revealed what he did not want us to see
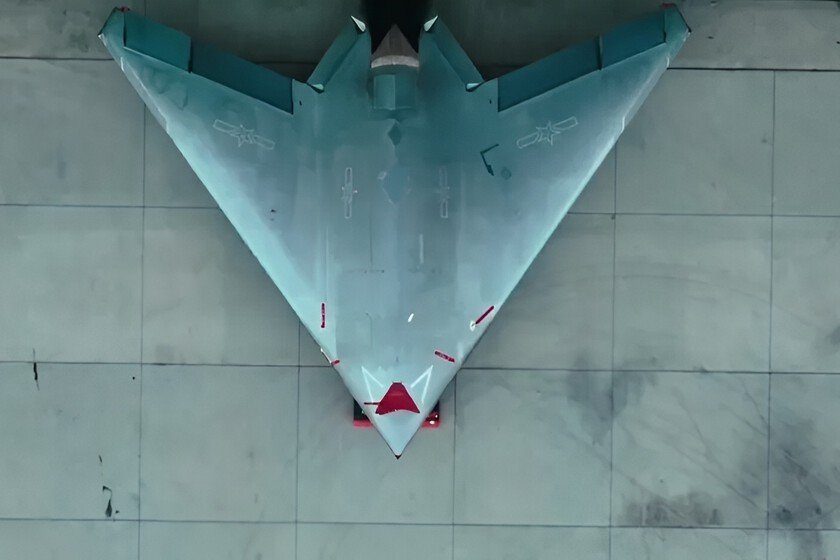
During the years of Russian invasion of Ukraine we had seen many tactics that copied techniques and weapons from the past. For example, the use of the Davis cannon of the First World War, or the application of anchored shotguns on airplane wings. In fact, the use of shotguns and rifles from the last century has become a normalized scenario over the months due to the lack of modern artillery. Russia has now shown in a video how to hunt drones. Although he has also inadvertently revealed another detail. Shotguns in the front. The silent battle that is fought every day between Russian boats and swarms of FPV drones in the Dnieper has revealed now one of the most unexpected tactical turns of the war: the resurrection of the shotgun as a survival tool on a battlefield dominated by sensors, radio waves and munitions costing just a few hundred dollars. The viral sequence recorded from the helmet of a Russian marine, it offers a deceptively heroic portrait of a crew sailing at full speed through narrow channels while shooting down drone after drone (up to 13), although the meticulous analysis of each fragment shows that the initial epic falls apart as soon as the details are examined and what is behind it is understood: a fragmented combat, recorded on different days, in which the probable casualties are left out of the shot and where the electronics have as much weight as the shots. The mirage of the mission. They counted it analysts at Forbes. What seems like a single continuous episode in reality It’s a montage of multiple confrontations, where the sky changes color between shots and where the marines shoot at both real threats and invisible threats, lost among interference and gusts of wind. The barge sails while three shooters with semi-automatic shotguns, an automatic rifle and a light machine gun try to keep at bay drones that explode at the slightest contact. Thirteen devices fall, but the editing hides both the failures and the side effects. Two explosions centimeters from the hull leave doubts about possible injuries that are never shown, while a revealing detail (a Marine who already has a tourniquet placed preventively on his thigh) speaks of very specific expectations: the probability of being hit is not a hypothesis, but an assumed fact. Elite unit supported by electronic warfare. Forehead to the ‘Mobiks’ sent to slaughter with weeks of instruction and precarious material, this unit stands out for modern equipmentfor the shooting discipline and for the hidden arsenal that really explains part of their survival: a antenna constellation electronic warfare mounted on the boat. These inhibitors, with a range of between 50 and 100 meters, turn many drones into uncontrolled projectiles that fall by pure gravity. The shotgun just finish what electronics has already weakened. In an environment where FPV munitions explode even when the operator loses signal, the difference between living or dying depends not solely on aiming, but on the ability to blind the drone before it gets too close. That is why the shots show drones collapsing far from the effective range of the shooters: they did not fall due to an accurate shot, but due to interference. The limits of the shotgun. That a shotgun can take down an FPV at close range is so true as misleading. The scene has fueled a narrative of false confidence that the soldiers themselves deny off camera. There are testimonies of teams that five drones were shot down followed to fall before the sixth when they ran out of ammunition, or patrols that aimed and fired until the last cartridge before a device entered through the window and destroy the vehicle. If you like, the arms industry has also adapted: Benelli already produces models specific “anti-drone”equipped with tungsten ammunition, and foreign donors have sent hundreds of semi-automatic shotguns to Ukrainian units. But the tactical principle does not change: a shotgun does not compete with the mass production of drones. It is a desperate tool to gain seconds in an environment where each drone costs less than a box of ammunition and where both armies manufacture them by the millions. Desperate defense. He video ends with the boat rescuing another group of marines: one is wounded, others advance with two weapons in their hands, and the scene, far from glorifying the resistance, underlines the true tactical message. The shotgun works, yes, but only when the number of drones is small, when the shooters are trained, or when there are active inhibitors and when luck is on the side. The complete story, the one that never goes viral, remembers that for every boat that returns, another does not. In the Dnieper War, the shotgun is not a weapon of air supremacy: it is the final spark that is fired when all else has failed, a defense of last resort against a swarm cheap and numerous which is redesigning the way armies move, attack and survive. A shotgun may give you time, but in an FPV-saturated front, that time may not be enough. Image | RUSSIAN MOD In Xataka | Ukraine has just reduced what took days to two minutes. And then he began to crush the most feared Russian weapon: his kamikazes In Xataka | The new peace plan in Ukraine has been reduced to 19 aspects. The problem is that the key point measures 900 km