The US has had a grain for “Iran”. The United Kingdom does not allow its bombers to enter a secret island that is key to the attack
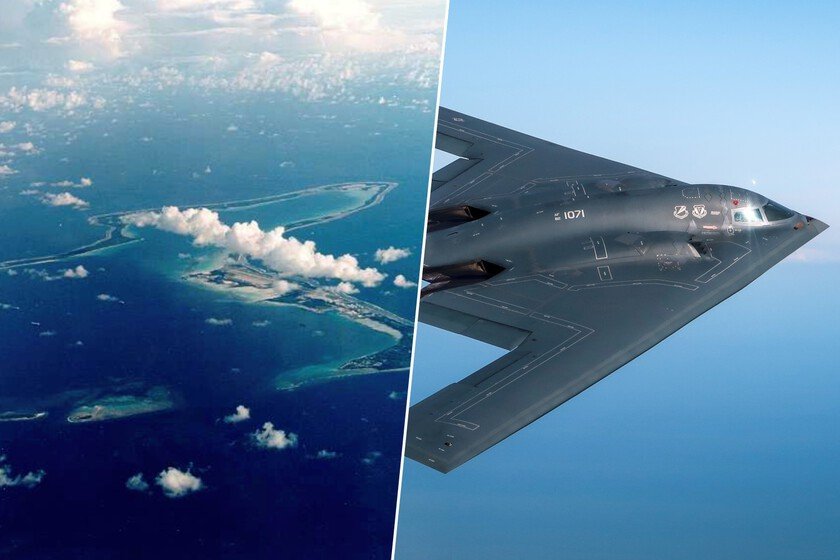
Since the Cold War, many of the great powers have understood that modern wars do not begin when the first plane takes off, but when secures access to the bases from which it will take off. Sometimes the deciding factor is not so much firepower, but the key that opens or closes a key clue at the exact location on the map. That is happening right now on a lost atoll. A problem with name and surname. The United States has had a major problem for “the Iran thing” and it is not in Tehran, but in the Indian Ocean. United Kingdom refuses to authorize the use of Diego García Island and the RAF Fairford base for a possible air campaign against the Islamic Republic, alleging that it could violate international law if it is a preventive attack. Without that permission, Washington loses two key platforms to project its long-range air power, just when the president has given an ultimatum to Iran and has hinted that in a matter of days he could decide between an agreement or a military operation. The secret island that sustains long wars. It we count some time ago. Located halfway between the east coast of Africa and the west coast of Indonesia, The island was part of the Chagos Archipelago. During the 18th century, it was colonized by the French as an agricultural settlement. So they took the Chagossians, descendants of slaves from Africa and India, to the islands to work on growing coconut trees for the production of copra (dried coconut meat). Over time, the locals developed their own culture and dialect, known as Chagossian Creole. By 1814, after Napoleon’s defeat, The island came under British control as part of the Treaty of Parisintegrating into the colony of Mauritius. Throughout the 19th century, life on the island continued with a small population dedicated to agriculture and fishing, but things were about to change with the beginning of the new century. The agreement. During the Cold War, The United States and the United Kingdom sealed an agreement. Both nations saw the island as a strategic location for a secret military base in the Indian Ocean. In 1965, the British separated the Chagos Islands from Mauritius, thus forming the British Indian Ocean Territory (BIOT), which also includes the other 57 islands of the Chagos Archipelago. By 1966, he signed a secret agreement with the United States, allowing the construction of the “secret” military base. Key node. Since then, Diego García is anything but any base, because he is one of the more strategic enclaves of the Pentagon in the Indian Ocean. Its central runway, its port capable of hosting nuclear submarines and its logistics infrastructure allow strategic bombers to be deployed, maintained and rearmed in sustained cycles. Without going too far, last year it already served as a pressure platform when several B-2s arrived in a clear message to Iran, and precisely that type of deployment is what is now conspicuous by its absence. That there are no visible bomber movements towards the island reinforces the idea that the british veto is conditioning military planning. Without bases there are no prolonged campaigns. The geographical difference is abysmal and explains the tension. From Diego García to Iran there are around 2,300 kilometers, from the United States more than 6,000. That distance sets the pace of departuresthe wear and tear of the crews and the intensity of the offensive. For a one-night operation you can fly round trip from Missouri, as was the case in previous attacks, but for a campaign a week or more against nuclear installations, military commands and missile launchers, advanced bases are needed that allow constant sorties to be generated. In other words, without access to the island and Fairford, the role of the B-2, B-1 or B-52 is greatly reduced and the plan loses volume. A clash between allies. The disagreement is not only technical, it is deeply political. London maintains that supporting an attack could implicate it legally if it knows the circumstances of an action considered unlawful, and the prime minister has marked distances with the White House. Washington, for its part, has responded hardening the tone and linking the refusal to the dispute over the future of Diego García within the Chagos Archipelago, whose status and possible transfer to Mauritius have opened a diplomatic rift. Thus, what began as a legal debate has led to a strategic struggle between historical allies. The war that is amplified without the key piece. Meanwhile, the United States continues to accumulate fighters, electronic warfare aircraft and resuppliers in the region, preparing the board as if the military option was still alive and imminent. It turns out that the heart of a prolonged air campaign is not the F-22s in transit, but those strategic bombers operating from a secure and nearby base. Yes UK maintains the vetoWashington will have more distant and less efficient alternatives, which would force the scope and intensity of the blow to be redesigned. In short, in full escalation with Iranthe piece that could do it all more simple For Washington it is precisely the one that blocks the movement today. Image | Department of DefenseRoyal Air Force, US Air Force In Xataka | One of the most remote islands was taken 60 years ago by the United Kingdom and the United States. Since then, what happens there has been a secret. In Xataka | If the most advanced US nuclear aircraft carrier maintains its speed, it will reach its destination on Sunday. Not good news for a nation