Amazon wanted its employees to continue using AI. They have just cut their losses by asking that “you do not use AI just for the sake of using it”
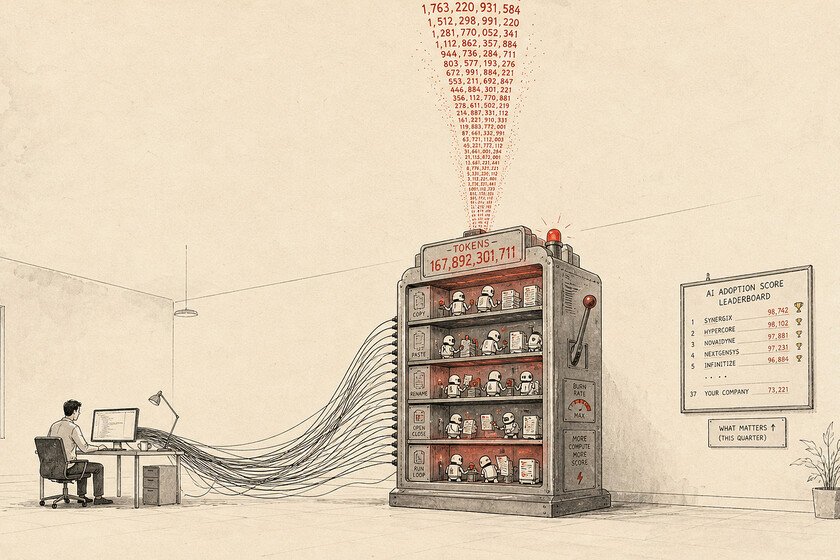
Amazon wanted to force its employees They will use AI as if there were no tomorrow. It implemented a tool that measured that usage, but after a few weeks the company realized something: people were using AI for absurd and worthless tasks. That has made Amazon make a decision forceful: abandon this initiative completely. what has happened. Amazon has had to cancel an experiment that measured the performance of its employees based on their use of corporate AI tools. The reason is simple: the engineers had begun to cheat and took the opportunity to automate completely useless and redundant tasks with the sole objective of climbing positions in the ranking. The labor scam has also absurdly increased the computing and infrastructure costs of the company itself, so the experiment has failed. The controversial Kirorank. The service in question was a scoreboard internally named Kirorank. It measured the activity of Amazon developers within Kiro, the “Claude Code of Amazon.” Amazon management wanted 80% of its programmers to use AI every week, an ambitious goal. What the developers ended up doing to score points with their bosses was deploying autonomous agents based on MeshClaw —the version of OpenClaw from Amazon—so that they would run processes in a loop and devour tokens for almost no purpose. The era of tokenmaxxing. Amazon Senior Vice President Dave Treadwell had to intervene this week before the staff to announce that developers no longer had to use this tool. Although he admitted that the experiment had originally been designed with “good intentions,” the practical result ended up being an economic hole due to the tokenmaxxingthat newly coined term that defines the action of artificially inflating the consumption of tokens to simulate productivity. “Please don’t use AI just for the sake of using AI,” the executive demanded of his engineers, urging them to focus on creating better products instead of burning server resources. Cost through the roof. Treadwell’s announcement is no small matter, because this shows that companies have realized that cost control is necessary with AI. Companies like Anthropic—of which Amazon is the largest investor and whose Claude model they use intensively—have recently migrated from flat monthly fees to a per-use pricing model based strictly on token consumption. With this new billing scheme, the fact that the engineers dedicated themselves to “playing” with the bots to rise in the ranking significantly multiplied the bill that Amazon had to pay. Meta suffered the same problem. The Amazon case is not an isolated event. In the Meta and Microsoft offices identical situations have been experiencedwith employees sabotaging internal AI usage rankings through massive token consumption. The irony for Amazon is tremendous: the company has been executing waves of massive layoffs to cut costs and be able to finance its gigantic investment plan in data center infrastructure and AI. Your theoretical capex for 2026 It is estimated at 200,000 million dollars. Lesson learned: AI must be used well. The failure of this “gamification” of work has ended with Amazon abandoning this experiment. To prevent developers from cheating again, a company team is going to change metrics. Instead of measuring raw token consumption, they will analyze so-called “normalized deployments.” From now on, the goal will be to measure how many times the interaction with AI results in useful lines of code that are truly integrated into the company’s products. In Xataka | Customers demand that a human solve their problem. The surprising thing is that if humans serve them they think they are an AI