also controls that of Portugal
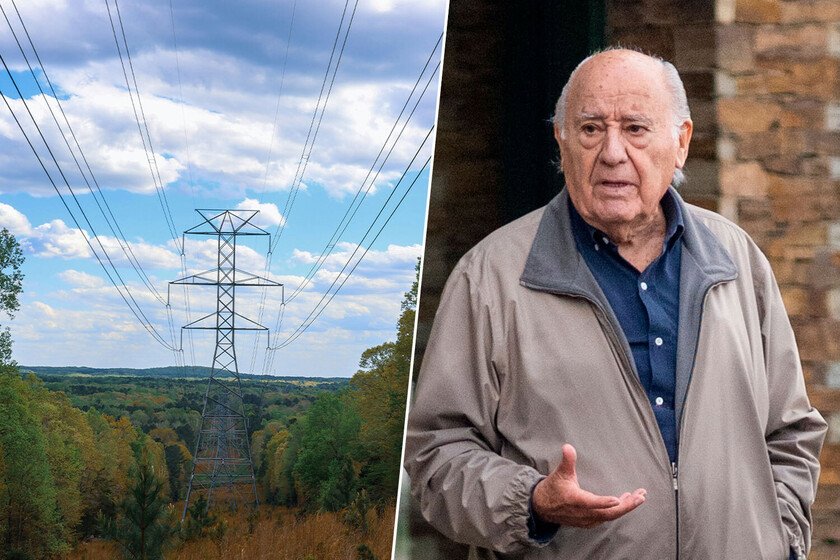
Amancio Ortega has decided to get fully involved in the Portuguese energy business. His investment vehicle, Pontegadeahas just raised its stake in REN (National Energy Networks), the operator of Portugal’s electricity and gas networks. This new movement in renewable energy field and the distribution networks leaves the founder of Inditex as the second main shareholder of the Portuguese energy operator, just behind the Chinese State Grid and places him in a strategic position in renewables throughout the Iberian Peninsula. The second largest shareholder of the Portuguese company. Pontegadea entered REN for the first time in 2021, when it agreed to purchase 12% of the capital that until then was controlled by the Mazoon group, linked to Oman Oil. That operation placed Amancio Ortega as the second largest shareholder in the Portuguese company, which manages key electricity and gas infrastructure in the country. With the new investment, Pontegadea has taken another step in consolidating its position in the renewable sector by adding an additional 1.7%, according to sources of Europa Press. Thus, Ortega’s investor reaches 13.7% of the Portuguese company’s total share capital. Pontegadea’s investment. During the second half of 2025, REN shares were traded between 3 and 3.4 euros per share, which makes the value of the new package of shares that Pontegadea has purchased currently between 30 and 38.5 million euros. This, added to the original 12% (which was valued at around 190 million euros at the time), leaves a stake in REN dear at around 314 million euros, in a company with a market capitalization of 2,292 million euros. Second largest shareholder. With 13.7%, Pontegadea consolidates itself as the second largest shareholder of REN, only surpassed by State Grid Corporation of China, which maintains 25% of the capital. The rest of the energy company’s shareholding is distributed in a more fragmented way: Lazard has dropped to around 6.6% (from the 7.7% it had before), Corporación Masaveu has 5%, the insurer Fidelidade another 5.3% and the Spanish operator Redeia completes the group of large investors with its 5%. This position as the second largest shareholder gives Ortega relevant weight in the company that operates energy in Portugal, without the need for iintervene in its direct management. In this way, Ortega benefits from the dividends and long-term growth of REN, a key player in the energy transition in Portugal. This is a very typical Pontegadea strategy that we have already seen in group investments in port entities and logistics infrastructures in which it enters with force, receiving stable income, but without complicating itself with its operations. He does not invest in energy: he is the one who controls it. In 2019, Ortega’s investor It did not have any participation in the energy sector. Seven years later, Pontegadea already has solid holdings and a strategy that looks to the energy future of the entire peninsula. However, Ortega’s position in this sector is not oriented towards energy generation, without the operators that control distribution networks. Amancio Ortega owns 5% of Redeia, the parent company of Red Eléctrica, which in turn is an investor in the Portuguese company REN. As in its Portuguese counterpart, Ortega’s investor is positioned as the second shareholder only behind the Spanish State, which through SEPI controls 20% of the operator. In addition, it maintains 5% in Enagás, the gas network manager in Spain, and another 5% in Enagás Renovables, where collaborates with Repsol in clean energy projects such as wind and solar parks. Strategy on both sides of the border. These positions form a block in Spanish and Portuguese infrastructure that prepares the ground for more renewables, storage and green hydrogen, all financed with Inditex dividends. The new investment in REN is not an isolated movement, but rather connects directly with what Pontegadea already has in Spain. REN collaborates with Enagás in the corridor hydrogen H2Medwhich connects Celorico da Beira in Portugal with Zamora, forming part of the great European commitment to green hydrogen. With 13.7% in REN and his positions in Redeia and Enagás, Amancio Ortega is at the heart of the networks that will move renewable energy throughout the Iberian Peninsula. In Xataka | Sandra Ortega rents hotels to hotels. Amancio Ortega has copied the model with a luxury hotel in Paris Image | Unsplash (Brandon Griggs), GTRES