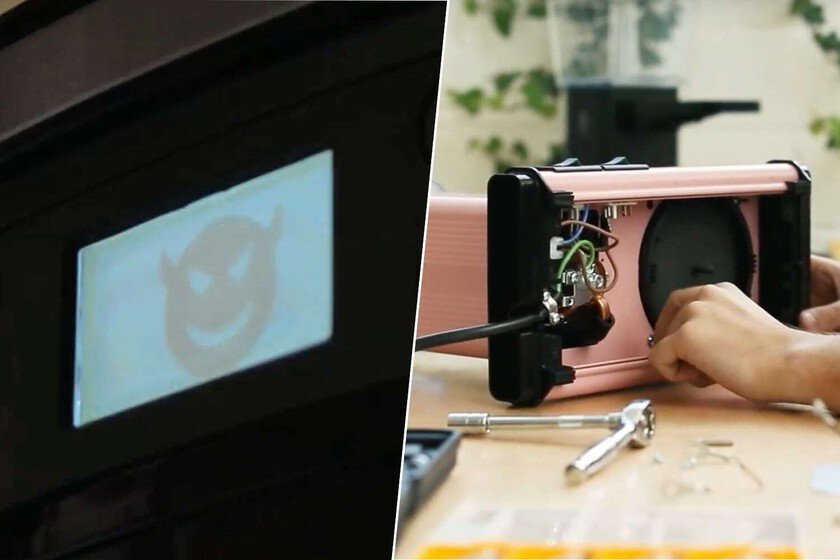
Few things give more anger than to play with an extremely simple device that does not respond exactly as you want. An example is the appliances that should be at our service, but sometimes they go from us, they are unnecessarily complex Or they have many functions, but not as simple as “don’t automatically turn off.” That is what a software developer was found to Buy a coffee makerand made the most logical decision. Return it? No: Hold it. And be careful, because that of ‘hacking’ the coffee makers is not so weird. Functions vs User. Gabriel Ciubotaru He is a software developer, but also an expert in cybersecurity and reverse engineering, among other skills. In a recent conference at the Defcamp 2024 (a relevant cybersecurity and hacking conference at European level), Gabriel told how he had acquired a coffee maker that he liked a lot, but that had a very annoying function: at 30 minutes of being on, he automatically went out. It is a function to save energy, and that is fine, but the problem is the enormous contradiction that arises when, every time it turns on, it performs a refined cycle that expels a moderate amount of water. In addition to water, it was a loss of time and Gabriel search between the options until finding a higher time limit: three hours. As he made a coffee every four hours, it was not adequate for his rhythm of life and decided to open the machine. Hold the coffee maker. The task seemed simple: extract the motherboard, locate the microcontroller and identify the system programmed to automatically turn off the machine and perform that refined process, change the firmware with the desired time value and reassemble the machine. The reality is that it found that component relatively easy, but the complicated thing was to find, throughout the code tangle, the lines that it should modify so that the coffee maker went out when he wanted. He did it, looking at a code that controls the warning icons that shows the coffee maker screen so that the user identifies his status following the instructions of the manual, so he modified those values, the modified code rose to the microcontroller and … ready, the coffee maker now works as he wants. I have explained it in a very simple way, but in Gabriel he gives all the details in his conference. He also comments that he has saved 30 seconds a day by investing 100 hours of work to hack the coffee maker, but that it is something that has been totally worth it because now it is the device that works as the user wants. More homemade projects. It is clear that not everyone has the resources, desire, time or interest in getting what Gabriel has achieved. Those 30 seconds, to many, would not be bother us, but what is also true is that there is an interest on the part of some users to hack their coffee makers in one way or another. One of the most popular coffee makers is Delonghi dedicates. It is what I have and has a series of default values that respond to the amount of coffee extraction time. For a pressurized portfilters like the one that carries the machine, they are adequate, but when you buy a portfiltros in the air, these values fall short and we have a way of programming a slower extraction based on combining its three buttons. It is something indicated in the manual, but what is not indicated is how to achieve a better milk foam. The sparkler included is functional, but not perfect. A trick to have more control over the process is to remove the metal part of the sparkler and keep the rubber, with a much thinner nozzle. Thus we can better control the process, but there is a problem: due to the pressure, the nozzle jumps. The solution? Set that mouthpiece to the coffee maker through a flangeand problem solved. Removing functions to the machine. That is a very simple modification, but there is another that is perhaps more interesting because it directly affects how coffee knows. In filter coffee makers, the most common is that the base has a resistance that keeps hot coffee for a longer time. This implies that coffee ‘cooks’ by extraction, but then continues to warm up with a high temperature base that modifies its flavor. It is not ideal, but even expensive machines (and that, supposedly, its manufacturers should know that it affects the flavor) implements it. Therefore, a common modification in this type of coffee makers is to open them and remove the cables that give energy to that resistance. It does not affect anything to the operation of the coffee maker when preparing coffee, but you eliminate that base that continues to cook the coffee once extracted. It is a modification that gives more “fear” than placing a flange, but it is worth it because, as I say, it has a direct influence on coffee. And as that modification there are many others, such as placing a more quality milk foamer in the aforementioned dedicate or changing the water pump pressure, Change the diffuser of water in a moccamaster … More serious implications. Ok, these cases are curious and allow to improve the functioning of the coffee maker, but really hacking a coffee maker is a serious thing. It is something that Martin Hron, Avast Security Researcher, demonstrated to the HAHKE AN INTELLIGENT COFFEE. Focusing on the first generation smartger, Hron got access to the system and realized that it worked as a unprotected Wi-Fi access point, with unbalanced connections and that allowed firmware updates without authentication. What did you demonstrate? Two things. On the one hand, which could rotate the mill without control, waste boiling water or emit beeps. He could also show a rescue message with a URL in which to make the payment so that the coffee maker ceases to behave … Read more