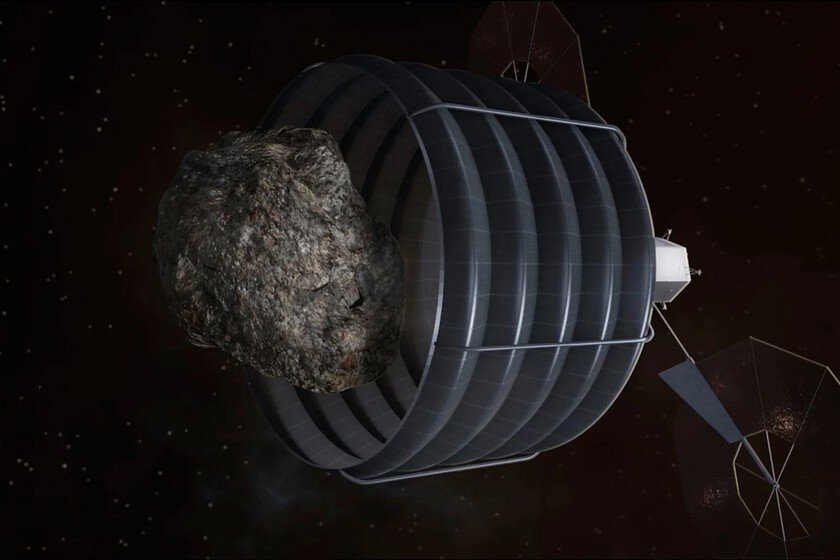
steal materials from the asteroid belt (with a stop at a gas station)
We haven’t built yet bases on the Moonbut already there are those who think in that future in which settlements can be built on Mars. If our satellite is a challenge, the red planet is already the pinnacle of complexity. Therefore, although there is still a lot of time for it to be viable, it doesn’t hurt to think about strategies. A good example is the proposal just made by a team of scientists led by aerospace engineer Serena Suriano. His proposal is based on one of the main problems that the space masons: the lack of materials. In the absence of suitable metals for construction there on Mars, they would have to be sought in the vicinity of the red planet. To do this, they propose “looting” the asteroid belt. It’s not that easy. In the asteroid belt There are metallic asteroids that could be mined for necessary metals such as molybdenum. But there is a problem. Traveling to these asteroids to take construction materials to Mars is not like taking the car on a Saturday to go to Ikea. In that case, the biggest handicap is the families that overcrowd the spaces. In the case of asteroids, the main problem is the orbital dance necessary to leave Mars, reach the asteroid and return. Luckily, these scientists consider that the problem could be solved with a couple of pit stops. An (almost) imaginary ship. When making calculations, it is normal to start from the parameters of a ship that actually exists. For this reason, these scientists have made simulations with an imaginary ship that is not the same, but looks like quite to the SpaceX Starship. The most powerful imaginable today. The ship in question weighs 120 tons, can carry a payload of 115 tons and hold up to 1,100 tons of fuel. This would mean a delta-v of 6.4 km/s. And what is that? The delta-v is a measure of the amount of effort necessary to carry out an orbital maneuver. In simpler terms, it is the change in speed that can be achieved by burning all the fuel in a ship. In this case it would be 6.4 km/s. The problem is that to reach the metallic asteroids that could be mined to build on Mars, taking into account the necessary orbital spins, a delta-v of 10 to 12.8 km/s would be needed. It can be solved. These scientists have designed a plan that includes two pit stops. The first would be on the metallic asteroid itself. Once the materials have been extracted, on the way back we would have to stop at a type C asteroid. These contain volatiles such as water and hydrocarbons, which would facilitate a process known as production on site of propellant. In other words, the type C asteroid would be used as a gas station, using its resources as propellant to continue the trip. If these stops are made, the necessary metals could be obtained with a delta-v of 6.4 km/s. The imaginary ship looks like Starship, but it is not the same 22 pairs. In total, there are 22 pairs of metallic asteroids and C-type asteroids in a 20-year window starting in 2040. This means that, from that moment, when it is assumed that trips to Mars and the construction of bases could already be viable, there would be more than 20 mine and gas station options to bring metals to the red planet. In total, 200 tons of metal could be obtained in that period. It may not seem like much if we consider that it is little more than the payload for a single trip. But fuel needs to be optimized. The loading process on site of propellant is carried out at a rate of 2 kg per day. To fill the tank it would take about 1,500 years. Logically, that is not viable, so you have to go with the tank half full and, therefore, adjust the payload. Why 20 years? For the trip to take place, it is necessary that the orbits of Mars and the asteroids are correctly aligned. It’s as if the road to Ikea only opens once every few years. Therefore, many trips could not be made. Building an entire base would take a lot of time, but it’s something you have to take on. A solution. If chemical propulsion is changed to solar propulsion or nuclearit would be much easier to extract metals from asteroids and, possibly, the deadlines would be shorter. However, these scientists have chosen to make their calculations with the only viable technology today. Maybe in the future the trip will be a little shorter than all this. Of course, building a base will continue to be a very, very long process. Many generations of humans would retire looking at those works. Image | NASA | SpaceX In Xataka | Elon Musk says it will take 1,000 Starships and 20 years to build the first sustainable city on Mars