China already has its “invisible hunt” ready for action, and twice
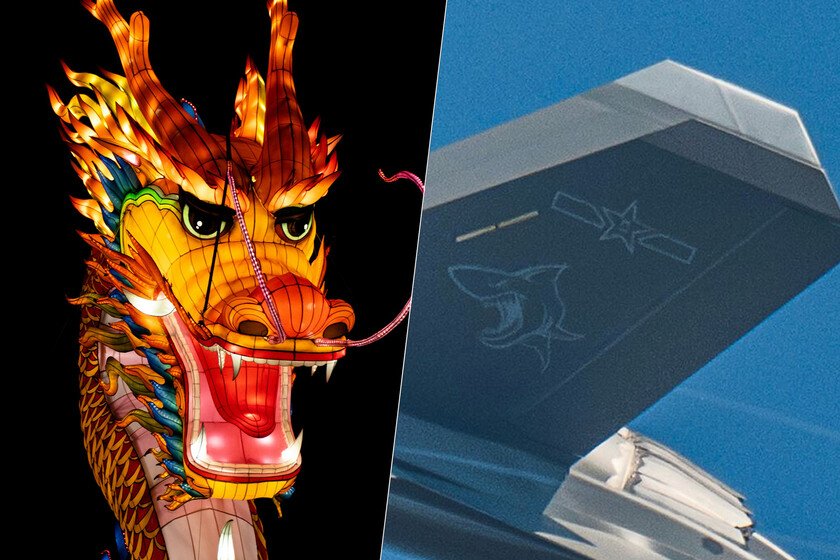
There is no official announcement. But China leaves clues again. This time they arrive from a Photography published in Weibo and replicated in x: two J-35 They fly in closed formation. What differentiates them from the prototypes seen so far are their construction numbers, “0011” and “0012”, clearly visible in the fuselage. It is a solid indication that the program has entered a limited series production phase, the typical LRIP prior to the operational deployment. LRIP registrations, emblems and a shark in the tail. The image seems to come from an official channel of the Chinese Navy. To the numbers are added other details that reinforce the hypothesis: national emblems in the vertical fins, a tactical gray free and a reason for a shark in drift. The specialist Andreas Ruprecht, Consulted by specialized means like War Zonehas repeatedly indicated these visual winks in Chinese naval aircraft. Click to see the publication in x The pilots also give clues: they carry bright blue helmets, exactly the type of helmet used by J-15 aviators in first-line units. All this suggests that these J-35 are already assigned to the Navy and in the validation phase prior to their entry into service. From FC-31 to J-35: the navalized variant that China needed. The J-35 derives from the FC-31, Shenyang’s furtive project for a more compact hunt than the J-20. The first navalized prototype flew in 2021; The second was seen in 2022 with a gray gray scheme of low visibility and, in 2023, blurred images of what could have been a third device emerged. Now, with the 0011 and 0012 specimens, we talk about units that already fit an initial serial configuration. The design is designed to operate from carckeners with catapults, such as Type 003 Fujianeven in tests. It is the logical step in an army that has been training in land facilities that simulates Catobar covers for years. Motors: WS-19 against WS-21, a puzzle still unsolved. The motor plant is still unknown. Some suggest that the land version, J-35a, already mounts the final WS-19, identifiable by darker nozzles. On the other hand, the naval specimens, with clear nozzles, could be driven by the WS-21, an evolution of the WS-13 used in the initial prototypes. There is no official confirmation and it is likely that Shenyang continues to adjust the engines in parallel to the progress of the program. Both airplanes carry a screwed Luneburg lens under their belly, a radar reflector that is installed when no total observability is required or when you want to mask the real firm of the device before third parties. Tests on aircraft carrier? For now there are no photos that demonstrate it. With airplanes apparently already in the hands of the Navy, the embarked essays are the next logical step if they have not already begun. There is also talk of a possible public presentation in September, during the acts by the 80th anniversary of the Japanese defeat in World War II. We will have to see if Beijing takes that occasion to exhibit it. One more piece in the puzzle of Chinese embarked air power. The J-35 adds to the KJ-600 early alert embarked the poaches that China has in development. Everything indicates that the country wants a more complex shipped air wing and comparable to that of the United States. It must know how long it will take to achieve real operational capabilities with this new generation of platforms. Images | Thomas Aseyroux | 沙丘里的回声 (Weibo) In Xataka | There is a city that maintains much of Russia’s economy in times of war. And it is on the Chinese border