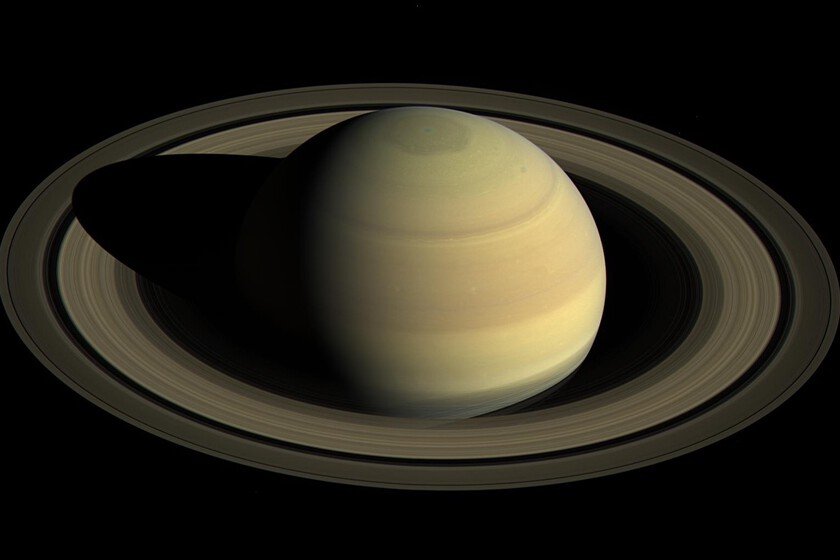
More than 40 years ago we discovered a mysterious hexagon on Saturn. Today there is only one possible explanation
If there is a planet within the Solar system as enigmatic as it is striking, it is Saturn. And not just because of their rings, probably caused by a collision of their moons. But it’s not the only thing that baffles the scientific community: if you look at Saturn’s north pole from space, you will discover a perfect geometric shape: a hexagon. 30,000 kilometers in diameter. To get the idea, two planets could fit inside it. Of that mysterious hexagon We know that it is there at least since 1981, when the Voyager 2 probe flew over the planet, leaving testimony of its existence. It is not that nature is not capable of making geometric shapes, but the hexagon is not exactly the most common. The latest and most solid hypothesis that attempts to elucidate what Saturn’s hexagon is to date was published in the Proceedings of the National Academy of Sciences offering a possible explanation: the internal dynamics of the planet’s atmosphere. The hypothesis. What the research team from Harvard’s Department of Earth and Planetary Sciences suggests is that the hexagon is not a surface structure, but rather is generated by rotating deep convection inside Saturn. The turbulence of the deep layers of its atmosphere generates vortices that push and bend a high-speed air current that surrounds the north pole, deforming it so much that it acquires its hexagonal shape. The hexagon is not the storm, it is the trace of what happens underneath. Qor why it’s important. Because we have been carrying around the mystery of the hexagon since 1981 and none of the previous theories fit as well as this one, capable of generating the hexagon from basic physics without artifice. Also, it answers a question: how far do Saturn’s winds reach? According to this model, to the bottom. On the other hand, if this explanation is correct, it changes the perception of how we understand the dynamics of giant planets, not just Saturn. Saturn hexagon with images from the Cassini probe. NASA/JPL-Caltech/Space Science Institute context. Before this 2020 theory, there were two clear sides: The forced Rossby wave proposed that the hexagon was an atmospheric wave held in place by an anticyclone, visible south of the pole in Voyager 2 data. When the Cassini probe arrived at Saturn in 2004, there was no trace of that anticyclone. That of the surface jet suggested that the hexagon was a surface wind that, when it becomes unstable, undulates and adopts a polygon shape. The problem was that it needed a starting current. Furthermore, it places the phenomenon in superficial layers, which contradicts the gravitational data of Cassini’s Grand Finale whose gravitational data suggest that Saturn’s winds maintain their intensity up to 100,000 bars of pressure. In both cases, they all reproduced the hexagon if you already gave them a base wind, but none of them generated it from scratch. How have they done it. The methodology is quite abstract, but roughly what they did was simulate a slice of Saturn, spinning it and heating it from below and letting physics act. No winds or hexes in the initial setup. So much the code used in the simulation like the data They are openly available, so anyone can reproduce and verify the results. Yes, but. The hypothesis developed by the Harvard team may be the best so far, but the paper itself recognizes Some objections to take into account. Thus, the simulation polygon is faster than what happens in reality, something that could be solved with a more powerful simulation. The simulation polygon moves faster than what happens in reality, something the authors attribute to the computational power available. Furthermore, the simulation only tests specific conditions and for a relatively short time: no one has yet verified whether the result holds under different parameters or on longer time scales. In Xataka | We have just discovered a true cosmic anomaly: an “invisible” galaxy made up almost 100% of dark matter In Xataka | A new “solar system” has just been discovered. There’s just one problem: it shouldn’t exist. Cover | NASA/JPL-Caltech/Space Science Institute