Leica is teaching Xiaomi everything it knows. When the student no longer needs the teacher, the agreement will have fulfilled its function
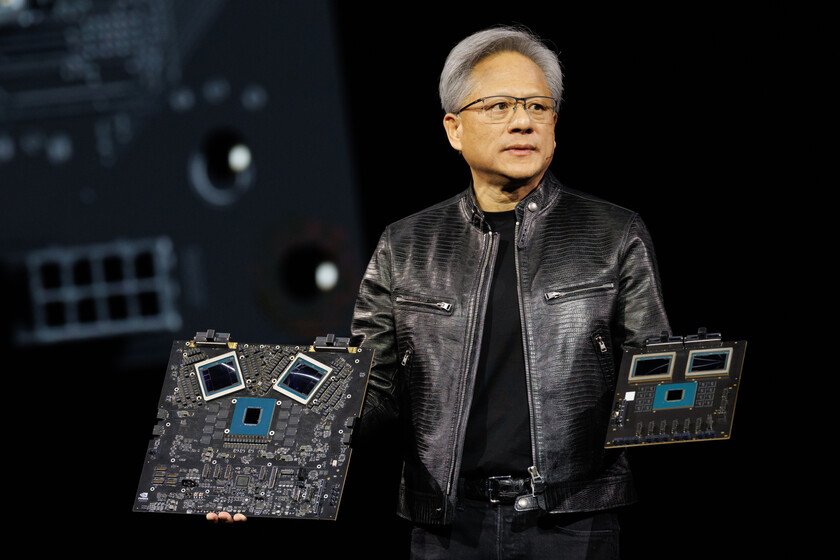
This week there have been two presentations of flagships which, seen together, say something interesting about where each manufacturer believes the industry is going: Samsung introduced the Galaxy S26 Ultra like an AI exhibition: three integrated assistants, the mobile phone as an external brain that anticipates what you are going to need before you ask for it. A few days later, Xiaomi presented the 17Ultra. And his big argument was not AI. It was the camera. And inside the camera, above all, it was Leica. It is advisable to take this collaboration seriously before reducing it to a marketing seal, because it is not. We had the opportunity to check it out in a session with TJ Waltonglobal product manager at Xiaomi, and Pablo Acevedoat the head of Leica’s mobile division. A round with around twenty journalists from Japan, Germany, France, China and other markets, in which Xataka It was the only Spanish medium. Left, TJ Walton. Right, Pablo Acevedo. Image: Xataka. I opened the question session with a very direct question: what does this co-creation model mean in reality, and at what point in the process does Leica come in? Acevedo’s response was also direct: “We are involved from the beginning, from the conception of the device, when we define the concept of what it should be.”. It is therefore not a certificate that is awarded at the end. It is shared engineering from the beginning: color tuning, contrast, physical adjustment of the lenses, testing of the final product… Walton summed it up: “Everything from the beginning to the end of the imaging experience on our smartphones is powered by Leica.” And still There is something in the details of the agreement that deserves attention, because Leica does not give the same thing to everyone. He Leitz Phonethe device that Leica markets as its own with Xiaomi hardware, includes ‘content credentials’, a certification of image authenticity that the Xiaomi 17 Ultra does not incorporate. When a Japanese journalist asked about this asymmetry, Acevedo was clear: “Authenticity is one of the important points for us. There are specific experiences aimed at professional photographers, those who really care about the smallest details of the photographic experience.” Said without euphemisms: Leica gives a lot to Xiaomi, but keeps for itself what it considers most defining of its identity. This ‘co-creation’ has limits. And those boundaries map out quite precisely where the partner ends and the customer begins. The presentation of the Xiaomi 17 in Barcelona just before the MWC. Image: Xataka. There was another moment in that same session that was like someone turned on the lights. When another journalist asked how the revenue from Leitz Phone is divided financially between the two companies, the response was: “I’m not sure if we can talk about that.” That is to say, The part of the agreement that would most reveal the true nature of the relationship is exactly the part that remains opaque.. Which is, in itself, an answer. Collaborations between equals do not usually have silence clauses on how the money is divided. OnePlus went with Hasselblad. I live with Zeiss. All different, all with the same underlying logic: a European name with decades of photographic history placed where the buyer sees it as soon as they take a Chinese phone out of the box. What they are buying is not only technology but the right to be given the benefit of the doubt in a segment where distrust of Chinese brands continues to be a real factoralthough decreasing. Each generation of product with Leica normalizes Xiaomi’s photographic excellence a little more. There will come a time when this standardization is complete, when the European buyer will not need anyone from the West to certify what he already knows. That day Xiaomi will not need to renew the agreement. And Leica will discover that she gave up part of her aura to someone who no longer needs it.while what Xiaomi gave in return (technology, scale, relevance in the smartphone market…) will have remained integrated into its products forever. And there is something there that is worth remembering. Leica has built its value on a very specific idea: scarcity. 8,000 euro cameras, limited production, a community of insiders who pay precisely because not everyone can… That’s the business. And now andHE same name appears on a device that sells tens of millions of units a year. Every Xiaomi 17 Ultra that comes out of a box does not destroy that aura, but it dilutes it a little. But there is something deeper than trade asymmetry. What happens, agreement by agreement, generation by generation, is a silent transfer of the center of gravity of technological prestige: For decades, European and American brands were the ones that certified the excellence of others. Now they are the ones who need someone to call them. Leica is not a victim in this process: it has made its decisions with its eyes open and has probably calculated its short and medium-term benefits well. But the long term has its own logic, and that logic says that when a historic brand becomes the endorsement that others need to grow, something in the balance of power has already changed. Although it is not yet noticeable in the price of their cameras. In Xataka | A week with the Xiaomi Mijia Smart Audio Glasses has shown me how great it is that your glasses are also your headphones Featured image | Xataka