For years we have learned to look with suspicion at the email that promises an unexpected refund, the SMS that asks us to update an account or the WhatsApp message that arrives too urgently. He phishing It has been recorded in us as something digital, glued to a screen, to a suspicious link or to a website that tries to look like that of our bank. But that image is falling short. The same logic of deception too can cross the door of the house inside an envelopeprinted on paper and with the appearance of an official communication.
The difference is not so much in the mechanism as in the context. Instead of waiting for us to click a link from our mobile phone, the attacker tries to take advantage of the trust we still place in certain physical communications. And, precisely, therein lies the risk. Paper can give a feeling of legitimacy that a suspicious email no longer always achieves, although the substance is the same as always: impersonating someone to push us to deliver information that we should not share.
Paper phishing: the old hoax has found another mailbox
A recent example Inés Zuriaga del Castillo shared it on LinkedInwho said he had received a physical letter at his home supposedly sent by Ledgerthe company known for its hardware wallets, physical devices for storing cryptoasset keys. According to its publication, the envelope included paper, an official-looking letterhead and an instruction to scan a QR with the supposed objective of updating the device and sending the recovery phrase. That last point is the most obvious red flag: the recovery phrase should never be shared.
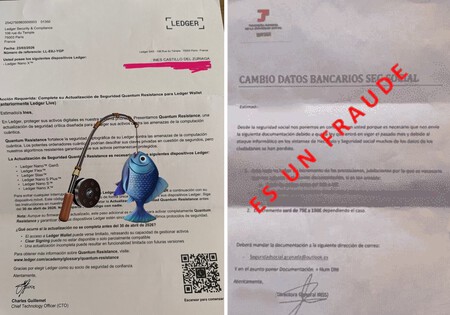
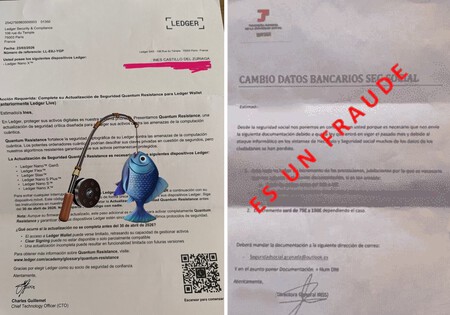
On the left, the case of a false letter sent in Ledger’s name. On the right, a fraudulent communication detected by Social Security.
Ledger has also warned of such attempts on its support page. The company describes a letter that presents itself as a “security check” notice and asks the user to scan a QR to enter their secret recovery phrase, supposedly to avoid security problems or interruptions in service. The company’s recommendation is clear: do not scan those codes, do not visit those links and never share the 24 recovery words. It is not a minor detail. With that phrase, an attacker can take control of the wallet and move the associated funds.
The case is not limited to the world of cryptocurrencies. Social Security has detected In Spain, a campaign of fraudulent letters aimed at beneficiaries of benefits and pensions, requesting personal documentation such as ID or a photo of the bank statement. The pretext, according to the organization, is that data would have been lost due to an alleged computer attack and that this information would be necessary to deposit an amount into the pensioner’s account after an increase in the benefit. The entity remembers that it will never request the sending of information or documentation by email, a sufficient clue to distrust this type of communications.
The two examples target different audiences, but share the same architecture. In the case of Ledger, the lure revolves around a wallet and a recovery phrase that should never leave the user’s control. In Social Security, the pressure is supported by a benefit, a pension and the promise of a pending income. They change the language, the impersonated entity and the type of data they are trying to obtain, but the underlying maneuver is identical: construct a communication that is credible enough for the victim to act before checking.
In the case of Ledger, the lure revolves around a wallet and a recovery phrase that should never leave the user’s control.
The question that remains floating is difficult to avoid: how does a letter like this arrive at a specific address. The truth is that personal data can end up exposed due to breaches in companies, suppliers or administrations, even if the user has done their part reasonably well: use strong passwords, activate two-step verification or be wary of suspicious messages. Without going any further, the AEPD reported that in 2025 he received 2,765 notifications of personal data breachesand noted that those that affected the largest number of people were related to ransomware and intrusions that led to the exfiltration of large volumes of information.
From there another piece of the wheel comes in: the stolen data is not always used only once nor does it remain in the hands of whoever obtained it first. As we already said in Xataka, documents such as a Spanish DNI could be found in illegal Internet markets for about 15 euros. This data does not explain the origin of the specific letters that we have seen, but it does help to understand something important: when personal information begins to circulate out of control, it can be reused in different frauds, with different formats and at times very far from the original breach.
There is a simple rule that works for both digital phishing and paper phishing: the more a communication pushes us to act quickly, the slower we should go. A letter requesting sensitive data should set off alarm bells. We should not scan the QR out of inertia, we should not scan the email it proposes and we would not call the phone number that appears as the only means of contact. What is recommended? First check on our ownon the official website or on public channels of the entity. It’s less comfortable, yes, but it’s also exactly what breaks the trap.
In the end, the format is almost the least important thing. It can be an email, an SMS, a WhatsApp message or a letter on letterhead. What changes is the scenario, not the intention: making us trust enough to deliver something that can later turn against us. That is why these types of cases are useful, even when we do not know all the details of their origin. They remind us that security does not begin when we detect a fake website, but one step before: when we decide not to automatically believe a communication just because it seems serious.
Images | Xataka with Grok | Ines Zuriaga del Castillo
In Xataka | How often should we change ALL our passwords according to three cybersecurity experts


GIPHY App Key not set. Please check settings