When Microsoft ends its support for security updates in its operating systems, it is not usually advisable to use a PC with said system unless it is for a specific and specific case. Eric Parker, content creator specialized in technology, wanted try with an experiment: use Windows XP today connected to the Internet and eliminating all types of protections.
As you may have imagined, the PC has become a magnet for malware. In fact, in just 10 minutes, the operating system was completely compromised. Parker also helped make this happen for educational purposes and to demonstrate how dangerous it can be to use an operating system like Windows XP today.
Windows XP without firewall and without NAT 10 minutes later: a magnet for malware
The expert configured a virtual machine with Windows XP Service Pack 3 on a Proxmox server, also disabling its firewall and NAT (Network Address Translation) settings and replicating the connection conditions common in the early 2000s.
To recreate this scenario, the researcher Completely disabled Windows XP firewall and assigned a direct public IP address to the system, exposing the machine without any intermediate protection.
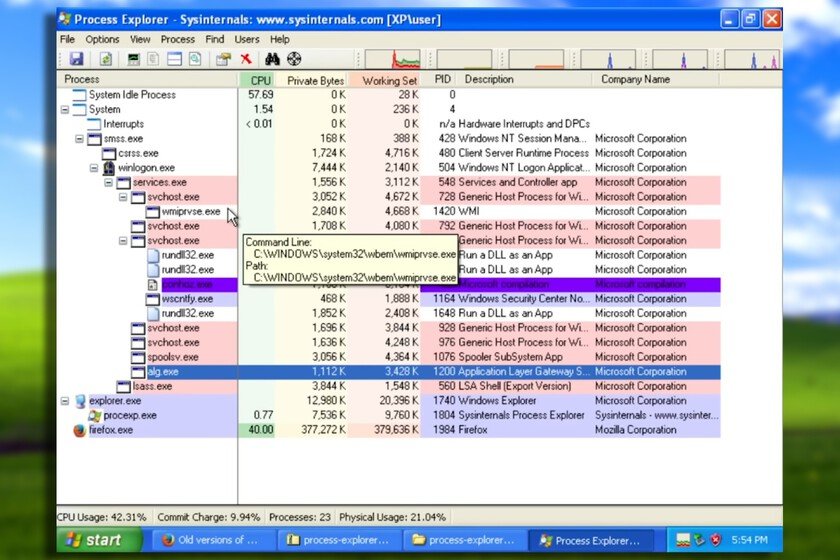
As seen in the video, in just ten minutes, the system showed the first signs of infection with the appearance of the “conhoz.exe” process in the Task Manager, which turned out to be a Trojan disguised as a legitimate component of the operating system.
After downloading a compatible browser and continued use of the system, in a short time we see how the PC starts to accumulate malware from multiple unknown sources. The system had been a victim of several Trojans and malicious programs running from temporary folders. He was also the victim of a rogue FTP server that allowed full remote access to files, DNS modification to redirect traffic to attacker-controlled servers, and the creation of additional user accounts for attackers to maintain access to the system.
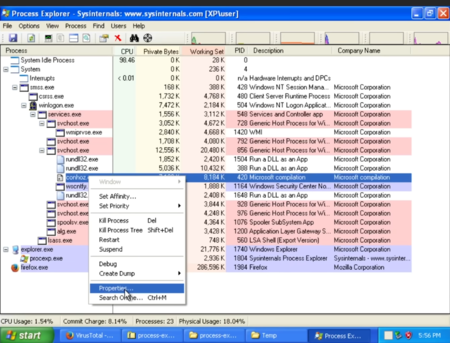
A whole string of malicious processes that ended up hijacking the PC. Image: Eric Parker
The key factor that allowed the rapid entry of all these malicious components was the vulnerability EternalBluepresent in unpatched Windows XP SP3. This security breach, which was later used by the famous ransomware WannaCryallows attackers to execute remote code without any user interaction.
Parker explains that tools like Nmap allow cybercriminals to scan the network for vulnerable systemsquickly identifying exposed and unprotected Windows XP computers.
A system that was crying out to be violated and a Windows 7 stronger than it seems
The content creator himself admits that the conditions were as optimal as possible to get malware: disabled firewall, direct connection without NAT and unpatched system. Under normal circumstances, with a basic home router and the firewall activated, Windows XP would be significantly more protected.
However, the risk does not disappear completely. The use of outdated browsers and the ease of privilege escalation on this operating system remain serious problems. And as shown in the experiment, once infected, The malware was able to automatically close security tools like Malwarebytes.
To contrast the results, Parker performed the same test with Windows 7 under identical conditions. Surprisingly, after ten hours of exposure, the most modern system showed no signs of infectionevidencing the significant security improvements implemented in later versions of Windows.
Now that official security update support for Windows 10 is ending soon, it’s good to take a look back and see how an outdated system can easily become compromised. Fortunately, today we have many more alternatives if we do not want to update to Windows 11.
Cover image | Eric Parker
In Xataka | FCKGW-RHQQ2-YXRKT-8TG6W-2B7Q8
This article was originally published in Genbeta in June 2025 and is part of Genbeta’s “greatest hits” that we will discover here in the coming weeks.

GIPHY App Key not set. Please check settings