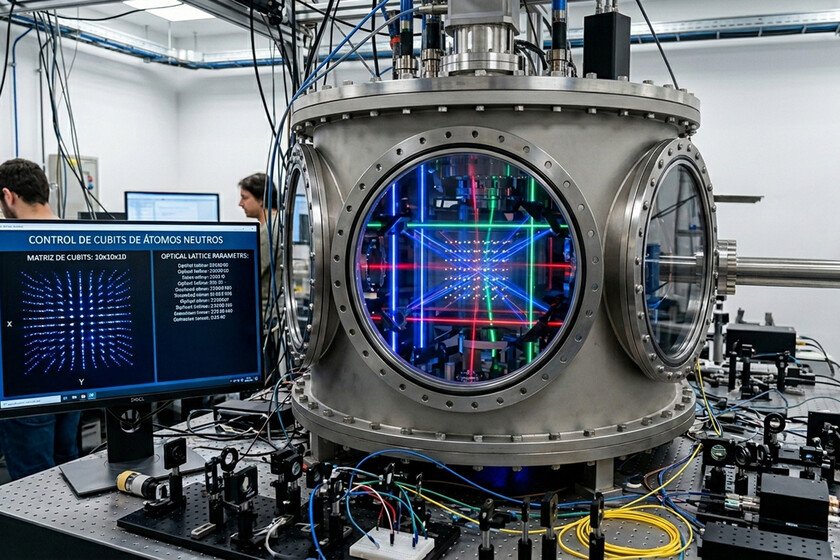
Just two weeks ago a group of researchers from the California Institute of Technology (Caltech), the University of California at Berkeley and the emerging company Oratomic published a scientific article preliminary in which they explore the capabilities of quantum computers of neutral atoms. These machines are an alternative to quantum computers with superconducting qubits and ion traps, and are still in an experimental phase.
However, these scientists have estimated that Shor’s algorithm can be implemented using a quantum computer equipped with between 10,000 and 20,000 qubits of neutral atoms. In fact, in their article they even propose a design with which in theory it would be possible break bitcoin encryption in a few days using 26,000 qubits of neutral atoms. In any case, these researchers are not the only ones who in recent weeks have alerted us to the ability to violate classical cryptography that quantum computers will acquire in a relatively short period of time.
At the end of last March, Google’s quantum artificial intelligence group published a study in which he demonstrates that the elliptic curve encryption used by Bitcoin or Ethereum, among other cryptocurrencies, can be overthrown using far fewer resources than initially estimated. According to these researchers, a quantum computer with less than half a million physical qubits will be able to decipher the algorithms used by current cryptocurrencies in a few minutes. In short, the scientific community has agreed that classical encryption technologies will be vulnerable before the arrival of large-scale quantum hardware.
The first steps to protect ourselves have already been taken
Quantum computing experts have known for several years that quantum computers they will end classical cryptography. That moment came in May 2024. A team of researchers from the University of Shanghai (China) led by Professor Wang Chao used a D-Wave quantum computer to successfully break SPN encryption (Substitution-Permutation Network), which is a cryptographic algorithm used to encrypt information.
This encryption is the cornerstone of, for example, the AES standard (Advanced Encryption Standard), which is used a lot. These scientists published the results of their research in an interesting article titled “Quantum Processing-Based Public Key Cryptographic Attack Algorithm with the D-Wave Advantage.” However, this is not all. And in mid-May 2025, several Google researchers posted an entry in the blog dedicated to the security of this American company in which they maintain a crucial premise: an RSA integer (Rivest–Shamir–Adleman) 2,048 bits can be factored in less than a week with a quantum computer of less than a million qubits.
A 2,048-bit RSA integer can be factored in less than a week with a quantum computer of less than a million qubits
Bitcoin, Ethereum, Solana and the other modern cryptocurrencies use a cryptography technique known as elliptic curve that is more robust, efficient and difficult to break than RSA, but its mathematical foundations are similar to those of the latter encryption algorithm. In fact, according to the Google scientists who authored the article I mentioned above, if future quantum computers will have a harder time breaking RSA encryption than initially expected, elliptic curve cryptography will also fall relatively easily.
So far we have talked about cryptocurrencies, but it is crucial that we do not overlook that encryption technologies play a fundamental role in our daily lives. In fact, WhatsApp and Telegram use them to encrypt our messages; banks turn to them to protect our transactions and every time we buy something on the internet it is encryption that is responsible for protecting our credit card information. These are just some of the applications of this technology.
The threat of quantum computers to encryption technologies is very real, but we have no reason to panic because many researchers have been working on the solution to this challenge for several years. In fact, most of the theoretical work has already been done. In 2024, the US National Institute of Standards and Technology (NIST) published an initial set of standards that includes a post-quantum key exchange mechanism and several post-quantum digital signature schemes. The work that has already been done invites us to foresee that the moment relevant quantum computers appear from a cryptographic point of view, the technologies that will be able to protect our information will already be ready.
Image | Generated by Xataka with Gemini

GIPHY App Key not set. Please check settings