You don’t have to have a house full of devices to depend on the cloud. All it takes is a connected robot vacuum cleaner so that some of its information passes through external servers and we can manage it from anywhere. The model has been standardized and, in principle, works. But that normality breaks down when questions arise about who can see what. That is what an American technology publication published regarding the DJI ROMO: A user claimed to have accessed data and activity from thousands of devices around the world before the issue was fixed.
Curiosity and risk. The story begins with something much more trivial than one might imagine. Sammy Azdoufal, an AI strategy manager at a vacation rental company, only wanted to control his own DJI ROMO with a PS5 controller “because it was fun,” as explained to The Verge. To do this, he developed a homemade application that began to communicate with DJI servers. The unexpected thing was that it was not just his vacuum cleaner that responded. Instead of a single device, thousands began to appear, spread across different countries, which recognized it as if it were its owner.
What I could see and control. What came next is what really changes the tone of the story. During a live demonstration, Azdoufal showed how his tool was detecting devices in real time: in just nine minutes he had cataloged 6,700 robots in 24 countries and collected more than 100,000 messages sent by them. Each one reported information every few seconds through a protocol called MQTTcommon in connected devices, indicating their serial number, which room they were cleaning, how far they had traveled or when they returned to the charging base.
As Azdoufal himself explained, he did not need to “hack” the company’s servers in the classic sense. What he did was analyze how his own ROMO communicated with DJI’s infrastructure and extract the private token associated with his device, that is, the credential that allows him to authenticate to the system. To decipher these protocols, he resorted to the well-known AI tool Claude Codewhich he used as support in the reverse engineering process. The problem, always depending on your version, is that once authenticated as a valid client, the servers did not properly limit which messages you could subscribe to receive.


The official version and patches. The company maintains that it detected the vulnerability in late January through an internal review and began remediation immediately. According to its statement, it deployed a first patch on February 8 and a second update on February 10 to cover nodes that had not received the initial fix. DJI admits “a backend permission validation issue” related to MQTT communication between device and server, although it says unauthorized access was “extremely rare.” It also highlights that the transmission was encrypted using TLS and that data from European devices is stored on AWS infrastructure located in the United States.
Questions on the table. If a user was able to detect that level of exposure almost by accident, one might wonder how these systems are internally audited and what controls are in place before a product hits the market. We are not talking about just any appliance, but rather a device with sensors, a camera and permanent connectivity within the home. Azdoufal himself even questioned the presence of a microphone in a vacuum cleaner. It is not a new debate: in recent years Other manufacturers have faced similar incidents with robots capable of transmitting video or storing images.
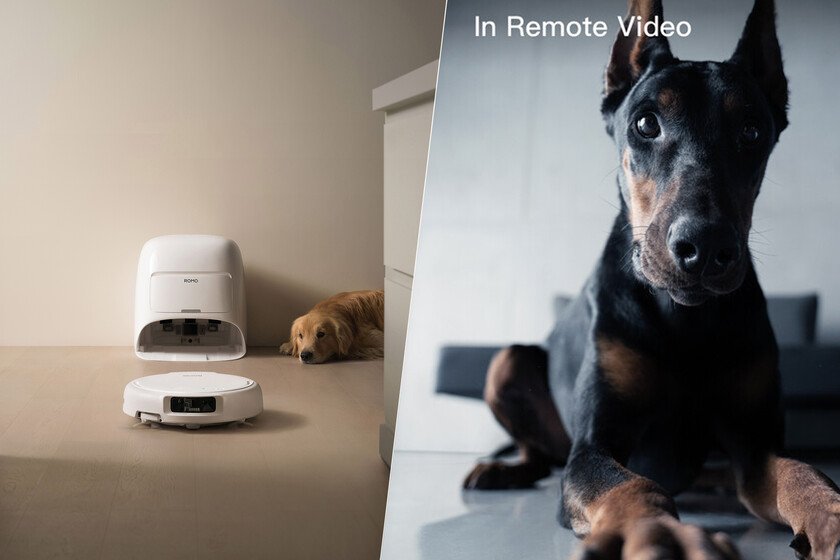
A change of scenery for DJI. After years dominating the air with drones and stabilization systems, the company decided to apply its engineering to domestic soil. The result was DJI ROMO, a robot vacuum cleaner that combines optical and LiDAR sensors to generate precise maps and avoid obstacles, supported by planning algorithms and the DJI Home app to manage zones, modes and alerts. It is not a simple mechanical appliance, but a connected platform that depends on continuous data to function with that precision. And that is where security takes on a determining role.
Images | DJI
In Xataka | How often should we change ALL our passwords according to three cybersecurity experts

GIPHY App Key not set. Please check settings