We trust our Password managers as if they were digital safes. But, According to expert Marek Tóthjust visit the wrong website and click where it does not correspond to put that armor at risk. The technique presented in Def with 33 does not point to applications, but to extensions we use daily In the browser. In his tests, he ensures that this gesture can activate an information theft system without the user perceiving it.
The research, made public in one of the main international conferences of computer security, documents how eleven extensions of password managers could be manipulated to filter data. Toth states that he notified the finding of manufacturers in April 2025 and that in mid -August several still still had corrections. The study includes practical tests, websites designed to demonstrate the failure and an estimate of the scope: about 40 million potentially exposed active facilities.
How the attack works and why it affects you
The technique described by Tóth is based on hiding the elements that the extensions insert on the page so that the user interacts with them without seeing it. With minimal changes in opacity or overlapthe attacker gets that The self -fulfilling is activated in the background. And there are several ways to achieve it, from manipulating the root element of the extension to altering the entire body of the site, in addition to variants by overlap.
The most delicate scenario appears when a trap website is not necessary, but it is enough to take advantage of a legitimate page with a security failure. In those cases, he explains, the attacker can capture login credentials. The risk increases because many managers fill data not only in the original domain, but also in subdomains, which expands the attack surface without the user noticing it.
According to data published by Tóth and collected by Socketon August 19, 1Password, Bitwarden, ENPASS, were continued as vulnerable Icloud PasswordsLastpass and Logmeonce. On August 20, Socket updated that Bitwarden had sent version 2025.8.0 with a patch, pending distribution in extensions. Among the managers who did apply corrective measures are NordPass, Dashlane, Keeper, Protonass and Roboform. Of course, this list can vary at any time if other companies publish arrangements after the dissemination.
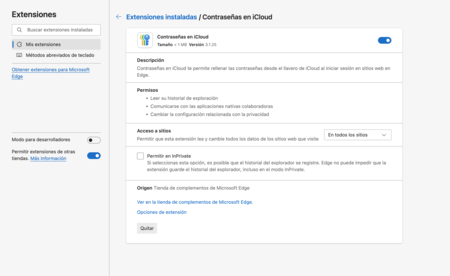
Extension of password manager for the browser
The manufacturers reaction was disparate. Socket points out that 1Password and Lastpass classified the ruling as “informative”, a category that usually implies absence of immediate changes. Bitwarden, ENPASS and Apple (Icloud Passwords) confirmed that They work in updateswhile Logmeonce did not respond to contact attempts. Some companies admitted the existence of risk, but related to external vulnerabilities at the sites visited.
While some developers decide how to act, Toth and Socket team agree that there are practical measures to reduce exposure. One of the most effective is to deactivate the manual self -fulfilling and resort to copying and paste. It is also recommended to configure the automatic filling only for exact URL coincidences, preventing it from working in subdomains. In chromium -based browsers, the use of the extension can be limited with the access option “When clicking”, so that the user explicitly authorizes each use.
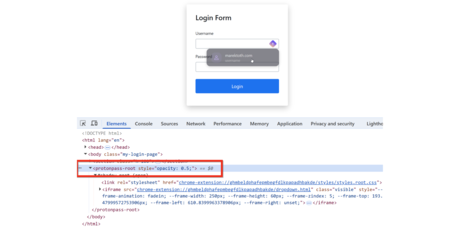
The researcher shows how it is possible to overlap invisible elements on the page to deceive the user and press the password manager without realizing it
Not everything is as immediate as clicking and losing everything. For the attack to succeed, the extension must be unlocked, the browser has not restarted and the user interact at the right time. In addition, the analysis focused only on eleven extensions. There is no evidence that All solutions The market is vulnerable, although the expert warns that the pattern can be repeated in other types of extensions.
The weak point is in the SUNthe internal structure used by websites to organize buttons, forms or menus. Password managers insert their elements there, and if a malicious page manages to move them, hide or force them, the user can end up clicking without realizing it. That same risk extends to other extensions such as cryptocurrency wallets or notes applications.
Images | Xataka with Gemini 2.5
In Xataka | How to change all our passwords according to three cybersecurity experts

GIPHY App Key not set. Please check settings