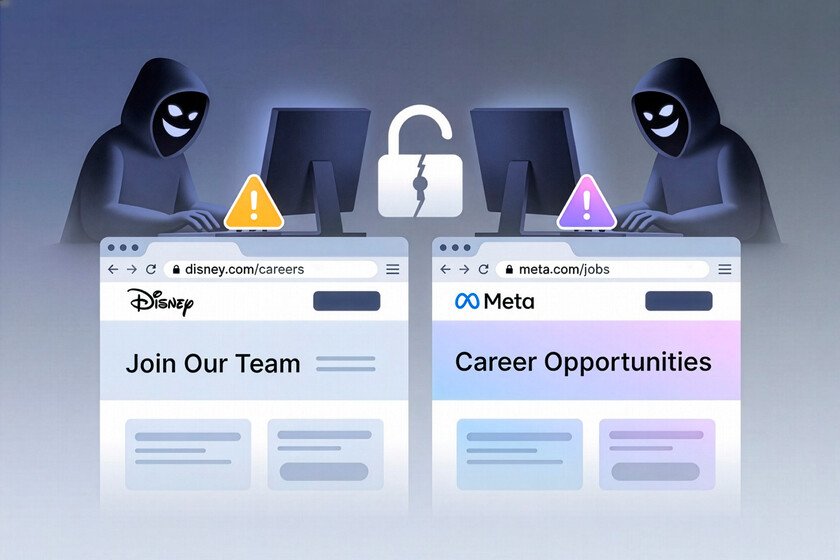
Looking for a job is already hard enough without having to be suspicious of every message that arrives in your inbox. And yet, that is exactly what the campaign that has warned about proposes. NordVPN: a trap set up to look like a real opportunity. We are not talking about a clumsy email or a sloppy website, but rather something much more refined, with names like Meta, Disney, Coca-Cola or Spotify as a claim. That’s the key to everything: they play with the illusion of those who believe they may be on the verge of an interview or a new job, when in reality they are entering into a fraud.
The investigation alerts of a campaign of phishing specifically aimed at job seekers. The attackers have set up an attack chain in several phases that impersonates large brands and seeks to take the victim to a very specific point: a false login screen with which they intend to keep their Facebook credentials. Let’s see in detail the strategy of these cybercriminals.
The mechanics behind fraud that imitates real selection processes
It all starts with cold recruitment emails, carefully written and with a professional tone that seeks to resemble real human resources communications. It is not a minor detail that some of these shipments are made through legitimate services such as Google AppSheetbecause not only can that help you avoid spam filters, it also helps make the scene more believable to the person on the other end. The trap, at least at the beginning, is not presented in a crude way, but with a very careful appearance.
From there, one of the most peculiar pieces of the entire chain appears: the so-called “HUB” domains. According to the investigation, these are pages that do not show their most sensitive content to anyone who enters directly. If a security analyst or an automated system visits that domain without coming from the specific link included in the email, what they find is a generic website, with hardly any visible activity. The truly important part is only activated when the visit arrives from that specific reference, which acts as a key and reveals the next step of the deception.
The next move of the campaign is to give the victim exactly what they expect to see after a convincing recruitment email: a website that looks like a job portal. The research explains that, after that first access, the user lands on a intermediate domain which simulates a legitimate job offer portal and where you can consult positions that seem real and associated with the company whose identity they are impersonating. The more the scene resembles a normal job search, the easier it is for the person to interpret everything that comes after as a logical part of the same process.
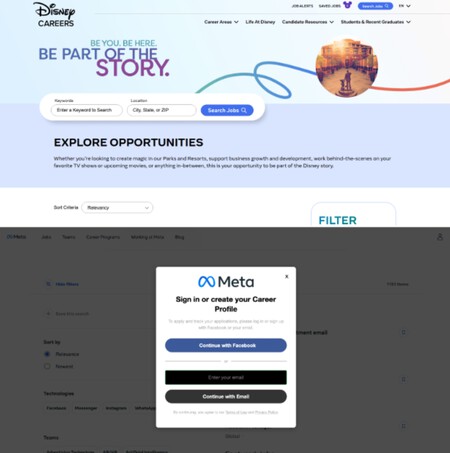
Campaign replicates legitimate job pages and uses Facebook login as hook
The decisive moment comes when the victim clicks on “Request” or “Send request”. That click does not open a job form or a next phase of the supposed selection process, but rather a phishing page that asks you to log in with Facebook to continue. That’s where the trap stops insinuating itself and begins to execute its true purpose. All of the above was designed to lead to that exact point, one in which the request may seem like another simple verification within the application, when in reality what is being delivered are the account credentials.
The supposed job opportunity was nothing more than the decoration of an operation with a much more specific purpose. According to the research, the final objective is steal Facebook credentials and thus obtain access to the victim’s account, with the possibility of also compromising other services connected to it. That’s why it’s a good idea to stick with a practical idea: before entering any credential, you should check the URL carefully, check that you are on the official domain, and be wary of any strange login.
Images | Xataka with Grok | NordVPN
In Xataka | AI is crucial for the US military. So he’s naming OpenAI and Palantir leaders as lieutenant generals

GIPHY App Key not set. Please check settings