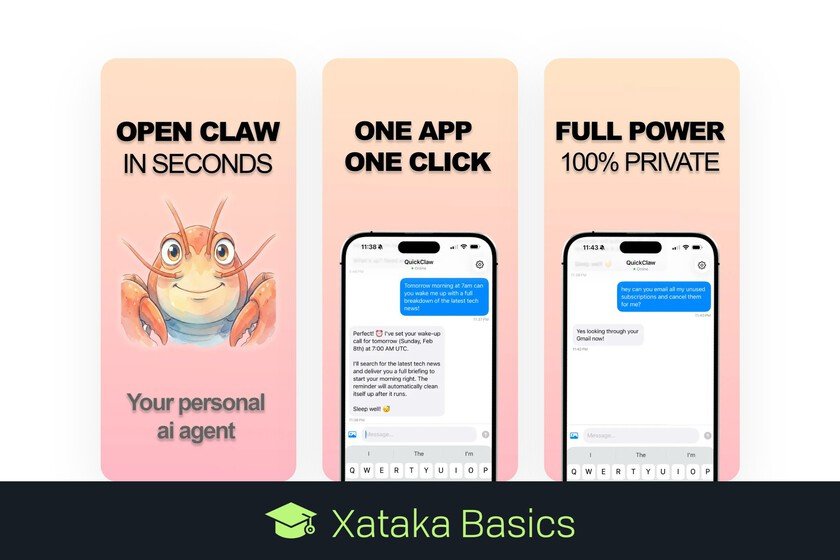
What is it, how does it work and how safe is this application to install OpenClaw on your mobile with just a couple of clicks
Let’s explain to you What is QuickClaw and how does it work?an application created by developer Max Blade to install OpenClaw easily on your mobile. Thus, you can have this popular AI agent without having to deal with APIs, servers and long configuration processes. The application does all this in a completely private way, and creating the agent within a virtual machine for your greater security. You just have to go to their website quickclaw.appclick on the download that is currently exclusive for iOS, and install everything with a single touch. What is QuickClaw QuickClaw is a mobile application that allows you to use OpenClaw easily on your mobile. Install OpenClaw It is a fairly complex process that can put many people off, and what this does is allow you to install it with a single click and without the need for complications or technical knowledge. Thus, you can have your own agent artificial intelligence on your mobile. This means that you will have an AI that does not limit itself to responding to what you ask or perform simple tasks, but can take control of your applications and perform tasks in multiple steps. All of this is done relatively safely. I say relatively because it will use an isolated workspace within your mobile, although the application will also needs access to a lot of your data to function, which may compromise your privacy. In exchange for this, you will have an application that will be able perform various types of tasks for yousuch as creating or editing files, browsing the Internet and taking actions there, managing your calendars, managing your reminders and more. How QuickClaw works The first thing you have to do is install the QuickClaw application, which at the moment It is only available for iOS in the App Store from Apple. When you install the app, you just have to launch it and An OpenClaw instance will be created and launched on a virtual machine “safe”, so as not to touch your device or its operating system. All this in just one minute. The process will then create a Gateway or user service that remains running, in addition to other components that allow OpenClaw to control applications, send messages and execute actions. All this will be done automatically with the recommended OpenClaw installer. This application is configured so that OpenClaw connect to Claude’s AIwho will be in charge of understanding your requests and carrying out the tasks you ask of her. All of this will be designed to be able to control the agent from your mobile using the app itself. What you can do with this app These are some of the tasks you will be able to perform from your mobile just by asking OpenClaw through QuickClaw: Write documents, essays and code, which are delivered as real files. Browse the web and research topics on your behalf. Set reminders and wake-up calls with personalized summaries. Read and manage your calendar and emails. Create, edit and organize files in your private workspace. Execute multi-step tasks autonomously. Remember the context of the conversations. How secure and private is the app One of the features of QuickClaw is to isolate OpenClaw in a virtual machine. This is an important security measureso that nothing the AI agent does can damage the operating system of your mobile device. OpenClaw is an open source agent, which makes it transparent and secure, people can check that it doesn’t do more than what it says it does. However, QuickClaw is not open sourceso you have to trust the word of its creator. Lastly, you should know that everything you make is sent to Anthropicthe company behind Claude. Currently this company is known for its commitment to offering ethical AI, although this can always change in the future. Your data within QuickClaw will be encrypted and anonymous. In addition, your conversations stay within your mobile, since everything runs locally. In Xataka Basics | Dangers of OpenClaw (formerly Moltbot or Clawdbot) and how to protect yourself from them before deciding to use it