Imagine a tool capable of bend the security of a mobile simply browsing a website, without downloading any file or accepting any permission. It’s scary, but if that cell phone is also an iPhonethings get even worse. It is not the argument of a conspiracy theory, it is reality and it has just destroyed Apple’s aura of invulnerability.
What has happened? Google security engineers have published a report detailing ‘Coruna’, a sophisticated hacking kit designed specifically to compromise iOS devices. According to the investigation, Coruna uses a chain of ‘zero-day’ vulnerabilities which give almost total access to the device. It’s going to be something similar to Pegasusbut even more sophisticated. The most disturbing thing is that it has been located in the hands of cybercriminals, but its origin appears to be in US government agencies.
What Coruna does. As we said, all you have to do is visit a malicious website for it to take action. Coruna’s architecture is based on an extremely complex exploit chain that takes advantage of flaws in the browser’s rendering engine and in the operating system core itself. In this way, it takes control of the iPhone silently, without the user downloading any files or accepting any additional permissions. The good news is that Apple patched one of these vulnerabilities with iOS 17.3, so if your phone is on this version or higher, you have nothing to worry about. However, despite these limitations, it is estimated to have infected tens of thousands of devices.
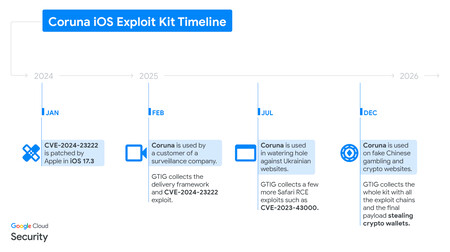
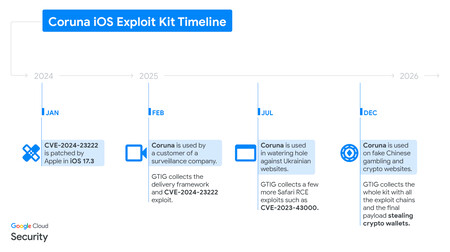
Image: Google
Timeline. In early 2025, Google first detected parts of this exploit chain that had been used by a commercial surveillance company. In the middle of the year he reappeared in a campaign against Ukraine attributed to Russian espionage and at the end of the year he made the jump to China, where he was hiding on fake websites about finance and cryptocurrencies. The kit stole cryptocurrencies and other data from victims, such as photos or email accounts.
Who has developed this. In statements to Wiredthe head of the security company iVerify, highlights that the code is “extremely sophisticated and its development has cost millions of dollars.” The most striking detail is that Coruna shares modules with the one known as “triangulation operation”another cyberattack targeting iOS discovered by Kaspersky and attributed to the NSA. At the moment it is a suspicion, but according to iVerify, the signs clearly point to it being the work of some US government agency or contractor.
How it has ended up in the wrong hands. It is the question that experts ask themselves and at the moment there is no answer, but there is a hypothesis. Zero-day exploits are those that the manufacturer, in this case Apple, has not yet detected and are the most expensive ones sold on the black market. The theory is that it was sold by an exploit broker to some foreign intelligence service and from there it made the jump to cybercrime organizations.
iVerify analyzed a version of Coruna and found that the code had been modified to install malware that emptied cryptocurrency wallets. These additions were “poorly written” and contrasted greatly with the underlying code, which fits with the theory that it was conceived by a very well-funded organization and then ended up in the world of cybercrime.
Image | Apple, edited with Gemini
In Xataka | Anthropic has become the Apple of our era and OpenAI our Microsoft: a story of love and hate


GIPHY App Key not set. Please check settings